Last Updated on March 13, 2024 by Asfa Rasheed
The COVID-19 pandemic forced a dramatic shift in the way Americans view work, life, and safety. The internet has many more users than ever before, and tons of people are logging on to work rather than commuting to an in-person office.
This surge in internet usage has made the internet a breeding ground for many cybersecurity hacks and data breaches. The increasing amount of information in data repositories means that a cybersecurity breach can be as damaging as a break-in, if not more.
If you run a business, you need to start caring about who has access to data in your company, who has administrator privileges, and how you organize your file system. This article will walk you through different sorts of users on the internet, and how you can organize their data usage so you don’t suffer a cybersecurity breach.
Table of Contents
What Does the Field of Data Access Entail?
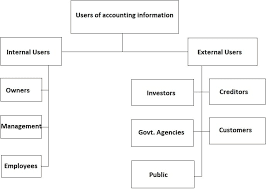
The field of data access measures different types of data users and determines how much access they should have to a particular system. On the one hand, you don’t want to keep important users away from data.
On the other hand, you don’t want users who spend large amounts of time on your database access to the most high-profile data:
Content Viewers
No matter how involved your business is, there’s going to be a segment of people who are only going to be viewing your content.
Generally, if people only need to view your content, they shouldn’t have access to a whole lot of data. You can’t be letting everyone on the internet know your business.
The highest amount of people need the least amount of access.
Discoverers
Discoverers are those who dive a little deeper than content viewers. These are your employees who work their way through your online world, without exactly creating any of it, or making any decisions.
They may leave comments and contribute to message boards however
Since these people are your employees, you want to grant them some access, but not too much.
Content Creators
Content creators are those people on your site or system creating content. They need access to a good deal of information so that they can know where to go next.
However, this information is very sensitive. You should only hire a small number of content creators and these creators should only be able to access this data through specific accounts.
Administrators
Administrators are those who oversee the creation of content and the structuring of a business. These people should have access to all of your data.
However, this should be an extremely small number of people. We recommend only having one administrator account, and giving it extremely limited internet access.
As you can see, digital access can get a bit complicated. This article will explain why it’s important to hire a digital identity management service.
Understand Access to Data
Anyone doing business in the 2020s has to worry about who has access to data. Structure your data so that most people have the least amount of access and vice versa.
For more articles like this, check out our “technology” section.